Resolv Issues Ultimatum to Attacker: Must Return 90% of Stolen Funds Within 72 Hours

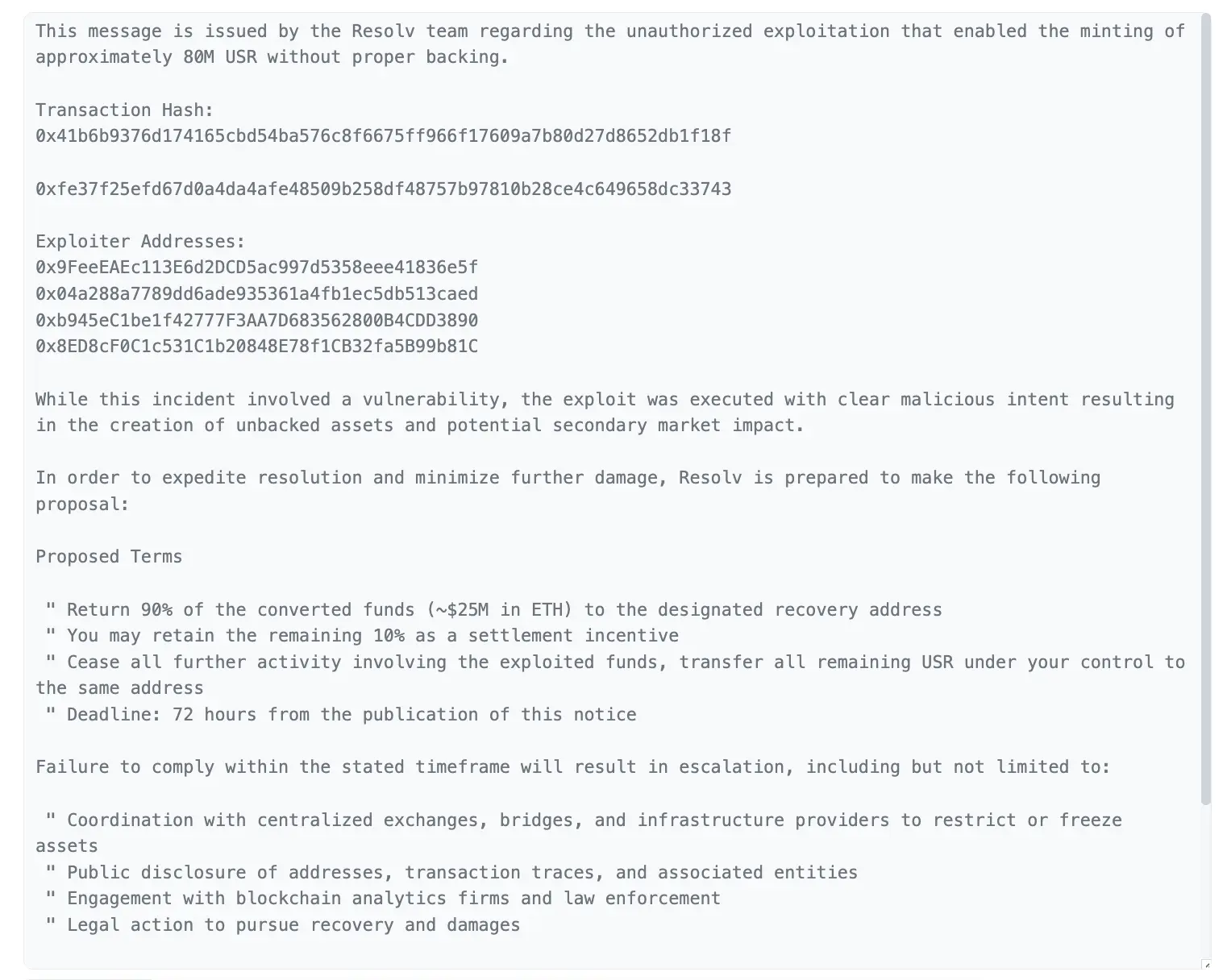
Resolv Labs announced on the X platform on March 24 that they have sent on-chain messages to the attacker’s address, officially proposing a settlement plan for the security incident that occurred on March 22. According to the proposal, if the attacker returns approximately 90% of the stolen funds (about $25 million USD in ETH) within 72 hours, they can retain the remaining 10% (about $2.5 million USD) as an incentive for settlement.
Settlement Plan Design: On-Chain Notification and White Hat Incentive Logic
 (Source: Resolv Labs)
(Source: Resolv Labs)
Resolv’s proposal follows the common “white hat incentive” structure in crypto security incidents: retaining part of the stolen assets in exchange for the attacker voluntarily returning most of the funds, while avoiding legal risks from subsequent law enforcement actions. This plan is directly encoded as an on-chain message sent to the attacker’s address, ensuring transparency and market traceability.
For the attacker, accepting the settlement means securing a certain $2.5 million USD while avoiding the increasing risks of law enforcement pursuit. Refusal will trigger multiple escalation measures simultaneously.
Four Escalation Measures After 72 Hours
Asset Freeze Coordination: Coordinate with centralized exchanges (CEX), cross-chain bridges, and infrastructure providers to freeze assets held by the attacker’s addresses, restricting the transfer and withdrawal of stolen funds.
Public Disclosure of Addresses and Transaction Paths: Publicly reveal the attacker’s wallet addresses and complete fund transfer paths, leveraging community tracking efforts to apply ongoing pressure.
Collaboration with On-Chain Analysis Firms and Law Enforcement: Work with blockchain analysis companies and relevant law enforcement agencies to enhance the chances of identifying the attacker’s true identity.
Legal Action: Take civil or criminal legal actions under applicable legal frameworks.
Background and Latest Recovery Progress
This settlement proposal is the latest development in the Resolv security incident. On March 22, the attacker accessed Resolv’s infrastructure using stolen private keys, minting approximately $80 million USD worth of unauthorized USR tokens, which were subsequently converted into about $25 million USD in ETH for cashing out.
According to Resolv’s latest update on March 23, the relevant smart contracts were quickly paused, and about 9 million USR tokens held by the attacker were burned to reduce further spread. The protocol currently holds about $141 million USD in assets, with the actual impact before pausing confirmed to be only around $500,000 USD in redemptions. The USR supply now consists of 102 million tokens before the incident plus approximately 71 million newly minted illegal tokens. A recovery plan has been initiated, starting from whitelisted users on March 23, allowing redemption of USR tokens before the incident.
Resolv strongly recommends suspending trading of USR and related tokens during the recovery process to avoid interference. Affected users should coordinate directly with RDAL through official channels.
Frequently Asked Questions
Q: What are the settlement terms Resolv proposed to the attacker?
If the attacker returns about 90% of the stolen funds (approximately $25 million USD in ETH) within 72 hours, they can keep the remaining 10% (about $2.5 million USD) as an incentive. If there is no response within the deadline, Resolv will initiate escalation measures such as asset freezing, address disclosure, law enforcement cooperation, and legal actions.
Q: How did the Resolv security incident happen?
The attacker accessed Resolv’s infrastructure using stolen private keys, exploiting a control vulnerability in the USR minting contract, minting about $80 million USD worth of unauthorized USR tokens, and converting approximately $25 million USD into ETH for cashing out. The underlying collateral of the protocol was not directly affected; the issue was limited to the USR issuance mechanism.
Q: What should USR holders pay attention to during the recovery?
Resolv strongly recommends suspending trading of USR and related tokens during the recovery process. Redemption services have resumed from whitelisted users since March 23. Affected users should coordinate directly with RDAL through official channels to ensure the recovery process is not disrupted.