Storj Technical Architecture: How Decentralized Cloud Storage Works
Storj employs a technical architecture that slices object data and distributes it across a global network of nodes, creating a distributed cloud storage system. By integrating a Satellite coordination layer, client-side encryption, and erasure coding, Storj delivers an S3-compatible storage experience for developers and enterprises. Rather than being a traditional “pure on-chain storage” solution, Storj uses a hybrid approach—“off-chain high-performance data plane + on-chain token incentives”—to organize decentralized resources into deliverable services through engineered processes.
As multi-cloud and AI data workloads continue to grow, the primary challenge for storage systems has shifted from simple capacity to the ability to deliver predictable, stable performance and security at a manageable cost. While traditional hyperscalers retain advantages in ecosystem maturity, they also introduce complications such as egress fees, complex cross-region policies, and vendor lock-in. Storj’s technical value lies in its combination of distributed nodes, default encryption, and parameterized redundancy, offering a compelling alternative. Public updates for 2025–2026 show Storj accelerating development in Object Mount 1.0, Cloud Compute, enterprise-grade compliance, and channel partnerships, with its technical scope expanding from storage to “storage + near-data computing.”
To understand Storj’s evolution, focus on three core themes: (1) how the network organizes and orchestrates heterogeneous nodes; (2) how data durability is maintained through encryption, sharding, and repair; and (3) how management and incentive mechanisms convert decentralized supply into stable commercial services. The following sections explore these pillars, incorporating recent acquisition and product upgrade developments to assess Storj’s future trajectory.
Storj Network Architecture and Node Distribution
Storj’s network consists of three layers: the client layer, the coordination layer, and the node layer.
The client layer handles data encryption, sharding, uploading, and download reassembly. The coordination layer, powered by the Satellite component, manages metadata indexing, node selection, audit billing, and repair scheduling. The node layer comprises global operators who provide capacity and bandwidth, forming the physical data plane. This layered architecture enables developers to use familiar object storage interfaces, while internal scheduling algorithms address node heterogeneity and geographic diversity.
Storj’s core strategy is not to centralize data in a few large facilities, but to build a “decentralized availability pool” using a vast array of independent nodes. This design yields two key benefits: (1) reduced single-point failure risk, as regional network fluctuations have less impact on overall availability; and (2) the need for ongoing node reputation evaluation and quality filtering to prevent low-quality nodes from degrading network performance. Thus, Storj’s technical challenge is not about maximizing node count, but about continuously assigning the right nodes to the right data fragments.
Recent disclosures indicate the platform is evolving from “single object storage” to a “distributed cloud platform.” The 2025 roadmap highlights Object Mount 1.0 and Cloud Compute, signaling an expansion beyond basic object read/write to include file-based access and compute-proximate deployment. The 2026 partnership with TenrecX further demonstrates a shift toward standardized enterprise procurement.
Data Sharding, Encryption, and Redundancy Mechanisms
Storj’s data protection begins at the client: objects are encrypted prior to upload, then divided into multiple fragments, and erasure coding is used to generate recoverable redundancy. This “encrypt first, then distribute” approach offers two main advantages: (1) node operators cannot access plaintext data, reducing the risk of data leakage at individual nodes; and (2) even if some nodes go offline or fragments are lost, the system can reconstruct the original object as long as the recovery threshold is met.
Compared to basic replication, erasure coding is more storage-efficient since it avoids full duplication of every object. However, it introduces higher operational demands, especially during node churn and data repair, requiring the coordination layer to continuously monitor fragment health and trigger rebuilds as needed. In essence, Storj’s durability is not static—it results from an ongoing “monitor-audit-repair” feedback loop.
This mechanism also encompasses metadata management, parallel fragment download scheduling, and reassembly verification. The main advantage is reduced single-path bottlenecks during cross-region access and large-object retrieval via parallel reads. The challenge: if node quality is inconsistent, tail latency and recovery times may increase. Storj’s competitive edge, therefore, hinges not just on encryption and erasure coding concepts, but on the ability to execute these mechanisms reliably at production scale.
Performance and Security Comparison with Traditional Cloud Storage
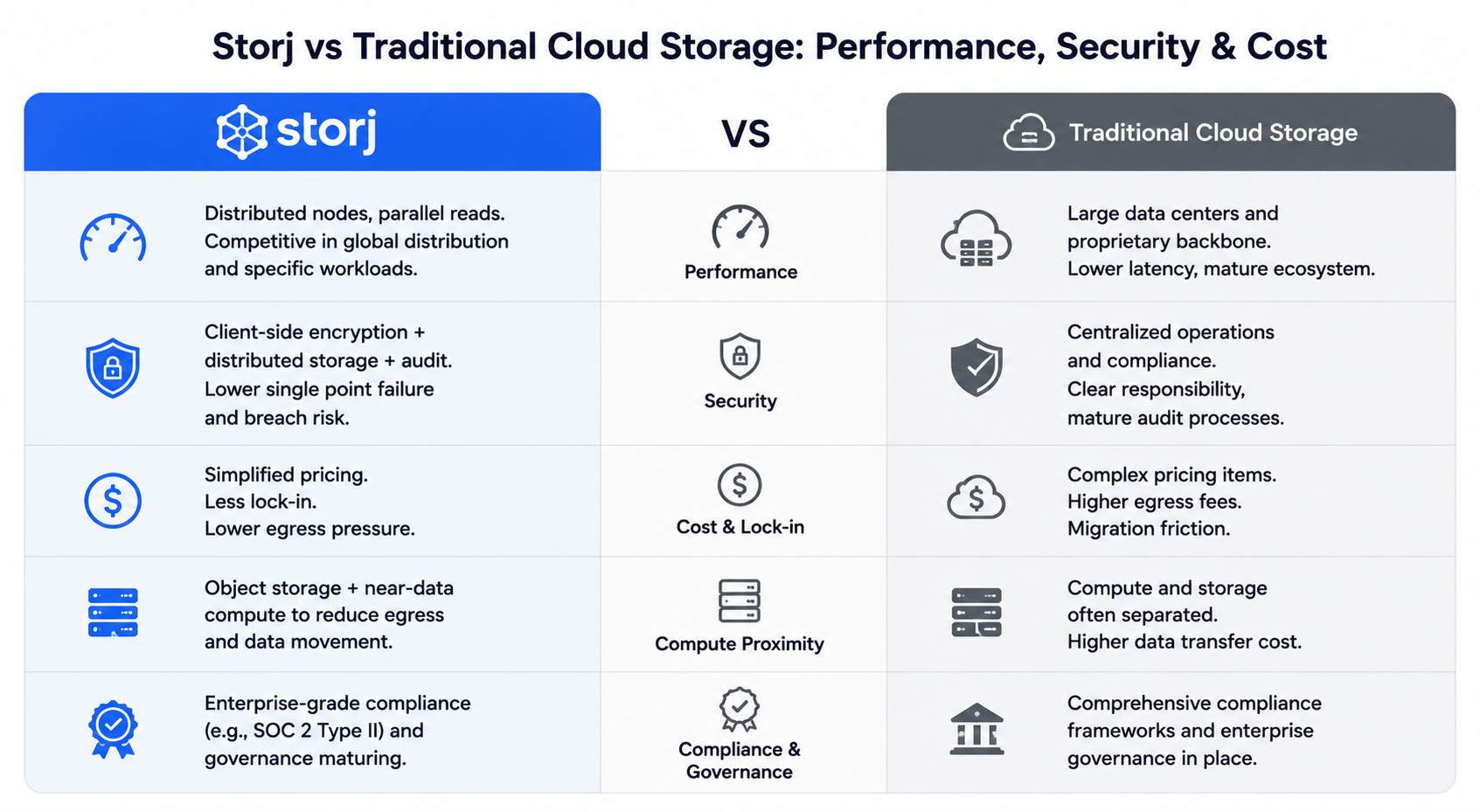
Storj’s performance and security trade-offs, compared to traditional centralized cloud storage, are best understood as structural choices rather than clear-cut wins or losses.
On performance, traditional clouds leverage large data centers and proprietary backbone networks, offering mature low-latency paths and ecosystem integration. Storj’s distributed node architecture and parallel reads can be competitive for global distribution and certain workloads, but performance stability depends heavily on node filtering and scheduling quality. Storj has recently highlighted its advantages in “download speed and cost structure,” and is pushing for synergy between object storage and near-data computing to cut egress costs between storage and compute.
On security, traditional clouds focus on centralized operations and comprehensive compliance frameworks. Storj, in contrast, emphasizes “client-side encryption + distributed storage + audit mechanisms.” The traditional model offers clear responsibility boundaries and established audit processes, while Storj’s approach reduces the risks of infrastructure failure and single-point data breaches. In 2025, Storj is emphasizing enterprise compliance, including SOC 2 Type II, signaling efforts to bridge the gap between decentralized architecture and enterprise governance standards.
Cost and vendor lock-in are where differences are most pronounced. Traditional clouds often feature complex pricing and migration friction; Storj’s narrative centers on “simplified billing, reduced lock-in, and lower egress pressure.” The real-world impact, however, depends on workload type—cost curves vary for backup, media collaboration, and AI data pipelines, and a single offer cannot substitute for a true TCO assessment.
Decentralized Management and Smart Contract Applications on Storj
Storj employs a hybrid management model: “protocolized rules + commercial operations.”
Decentralization is evident on the resource supply side, with nodes operated by multiple parties and capacity/bandwidth drawn from open networks. Centralized management is present in coordination services, product iteration, compliance auditing, and customer support. For enterprises, this hybrid is more practical than “purely centerless” models, as it preserves SLAs, ticketing, and contract interfaces. For industry observers, it demonstrates that decentralized infrastructure does not preclude organizational structure—it simply redistributes it across layers.
Smart contract applications are mainly found in tokenomics and verifiable fund flows, rather than on-chain execution of all storage operations. STORJ serves as the incentive token, linking node rewards, ecosystem settlement, and supply management. The platform regularly publishes token flow reports and, in 2025, will introduce mechanisms for buybacks and staking, aiming to enhance incentive sustainability and long-term participation. The technical challenge is not contract complexity, but whether incentive parameters align with network quality metrics.
In governance, Storj currently operates as an “open, transparent company governance + community feedback + on-chain verifiable data” model. Following the 2025 acquisition by Inveniam, public statements have emphasized business and token ecosystem continuity, suggesting future governance coordination within a larger data infrastructure context. This shift is likely to influence technical priorities—more emphasis on enterprise delivery, compliance, and cross-platform orchestration, rather than solely on-chain governance.
Future Directions for Storj Technology
The first direction is storage-compute synergy.
As Cloud Compute and near-data processing demand grows, future optimization will focus on unified orchestration of object storage, file access, and compute scheduling at the control plane, minimizing data movement and inter-service charges. For AI and media workflows, this is more valuable than simply expanding storage capacity, since true bottlenecks often exist in the “data-to-compute” pipeline.
The second direction is intelligent node quality and scheduling.
Long-term decentralized network performance is determined by node quality distribution. Future improvements will likely include more granular node reputation scoring, region- and time-aware fragment placement, dynamic repair task prioritization, and download scheduling sensitive to tail latency. As these capabilities mature, Storj’s global network performance consistency will improve significantly.
The third direction is enterprise usability and compliance.
Recent updates show ongoing enhancements to enterprise compatibility, such as backup ecosystem integration, tiered productization, channel partnerships, and simplified pricing. Technically, this means clearer permission models, robust audit and key management interfaces, and cross-region data governance. Industry trends like data sovereignty and hybrid cloud adoption will drive Storj to continually balance decentralized efficiency with compliance transparency.
The fourth direction is token incentives and network metric integration.
If buybacks, staking, and node incentives form a closed loop, the STORJ economy will be more closely tied to actual network usage. If incentives diverge from service quality, market volatility will impact ecosystem expectations. For the technical architecture, this is not a secondary concern—it’s fundamental to stable node supply.
Conclusion
At its core, Storj’s architecture is a “distributed resource organization system”: client-side encryption, erasure coding, and global node supply form the data plane; Satellite and operational systems constitute the control plane; and token mechanisms sustain incentives and value transfer. Storj is not a simple substitute for traditional cloud storage, but a distinct engineering path for different risk and cost profiles. With the 2025–2026 developments in acquisitions, product upgrades, and enterprise partnerships, Storj is evolving from early decentralized storage narratives to a “pluggable, compliant, and scalable” distributed cloud platform. Its long-term competitiveness will be determined not by any single technical term, but by the sustained alignment of network orchestration quality, enterprise-grade governance, and incentive mechanisms.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?